Multi-Factor Authentication (MFA) 101
October 11, 2022
Credential theft is now at an all-time high and is responsible for
more data breaches than any other type of attack.
With data and business processes now largely cloud-based, a user’s password is the quickest and easiest way to conduct many different types of dangerous activities.
Being logged in as a user (especially if they have admin privileges) can allow a criminal to send out phishing emails from your company account to your staff and customers. The hacker can also infect your cloud data with ransomware and demand thousands of dollars to give it back.
How do you protect your online accounts, data, and business operations? One of the best ways is with multi-factor authentication (MFA).
It provides a significant barrier to cybercriminals even if they have a legitimate user credential to log in. This is because they most likely will not have access to the device that receives the MFA code required to complete the authentication process.
WHAT ARE THE THREE MAIN METHODS OF MFA?

When you implement multi-factor authentication at your business, it’s important to compare the three main methods of MFA and not just assume all methods are the same. There are key differences that make some more secure than others and some more convenient.
Let’s take a look at what these three methods are:
SMS-BASED
The form of MFA that people are most familiar with is SMS-based. This one uses text messaging to authenticate the user.
The user will typically enter their mobile number when setting up MFA. Then, whenever they log into their account, they will receive a text message with a time-sensitive code that must be entered.
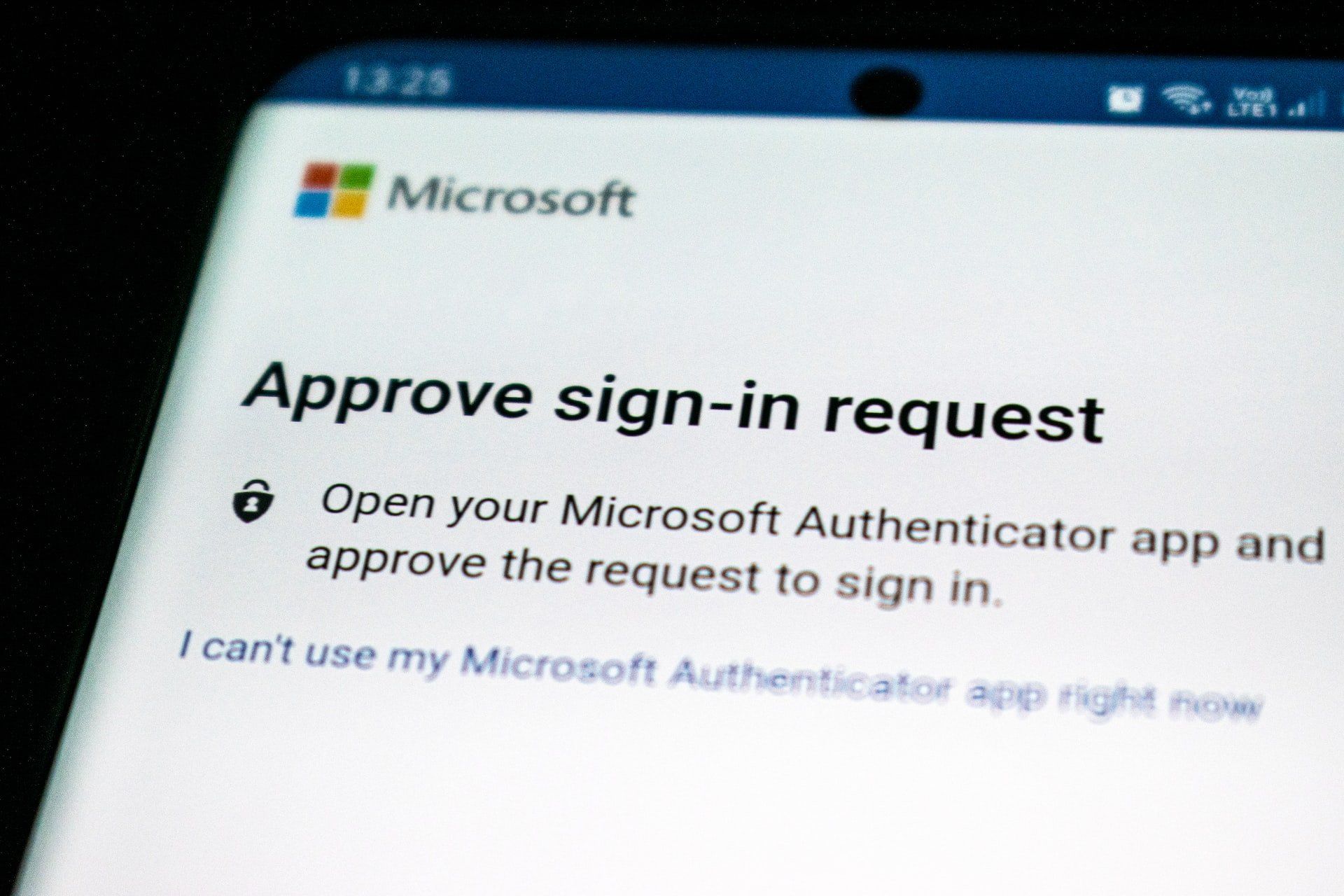
ON-DEVICE PROMPT IN AN APP
Another type of multi-factor authentication will use a special app to push through the code. The user still generates the MFA code at login, but rather than receiving the code via SMS, it’s received through the app.
This is usually done via a push notification, and it can be used with a mobile app or desktop app in many cases.
SECURITY KEY
The third key method of MFA involves using a separate security key that you can insert into a PC or mobile device to authenticate the login. The key itself is purchased at the time the MFA solution is set up and will be the thing that receives the authentication code and implements it automatically.
The MFA security key is typically smaller than a traditional thumb drive and must be carried by the user to authenticate when they log into a system.
Now, let’s look at the differences between these three methods.
MOST CONVENIENT FORM OF MFA?
Users can often feel that MFA is slowing them down. This can be worse if they need to learn a new app or try to remember a tiny security key (what if they lose that key?).
This user inconvenience can cause companies to leave their cloud accounts less protected by not using multi-factor authentication.
If you face user pushback and are looking for the most convenient form of MFA, it would be the SMS-based MFA.
Most people are already used to getting text messages on their phones so there is no new interface to learn and no app to install.
MOST SECURE FORM OF MFA?
If your company handles sensitive data in a cloud platform, such as your online accounting solution, then it may be in your best interest to go for security.
The most secure form of MFA is the security key.
The security key, being a separate device altogether, won’t leave your accounts unprotected in the event of a mobile phone being lost or stolen. Both the SMS-based and app-based versions would leave your accounts at risk in this scenario.
The SMS-based is actually the least secure because there is malware out there now that can clone a SIM card, which would allow a hacker to get those MFA text messages.
A Google study looked at the effectiveness of these three methods of MFA at blocking three different types of attacks. The security key was the most secure overall.
Percentage of attacks blocked:
- SMS-based: between 76 - 100%
- On-device app prompt: between 90 - 100%
- Security key: 100% for all three attack types
WHAT’S IN BETWEEN?
So, where does the app with an on-device prompt fit in? Right in between the other two MFA methods.
Using an MFA application that delivers the code via push notification is more secure than the SMS-based MFA. It’s also more convenient than needing to carry around a separate security key that could quickly become lost or misplaced.
LOOKING FOR HELP SETTING UP MFA AT YOUR COMPANY?
Multi-factor authentication is a “must-have” solution in today’s threat climate.
Let’s discuss your barrier points and come up with a solution together to keep your cloud environment better secured.
Contact us for a 15-minute, obligation-free consultation to discuss how our
cybersecurity services
and
managed cloud services can help keep your business protected from threats.
Article used with permission from The Technology Press.